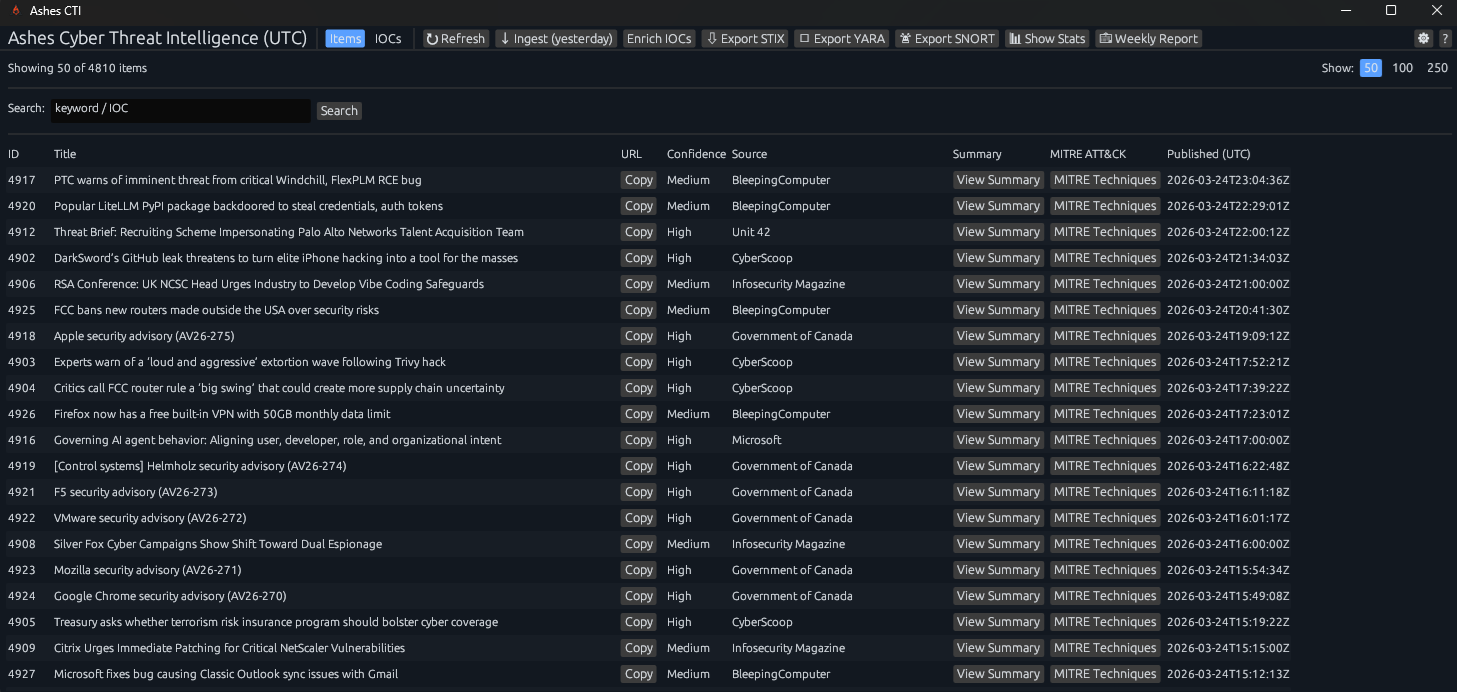
Ashes CTI – Threat Intelligence Workstation
A Windows-native threat intelligence workstation designed for SOC teams and restricted environments. Intelligence is processed locally, enabling analysts to extract, validate, and operationalize indicators without reliance on continuous cloud connectivity.
No cloud dependency. No telemetry. Fully local intelligence processing.
What is Ashes CTI?
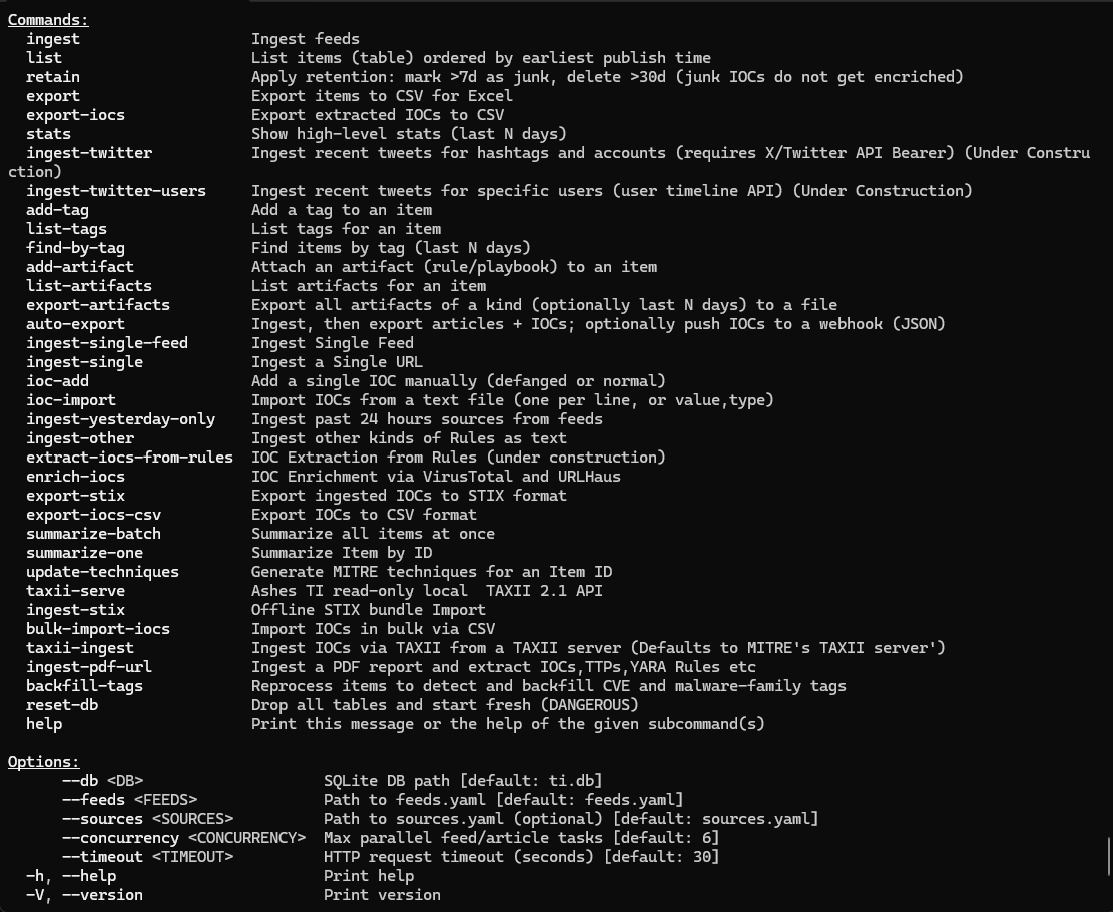
Ashes CTI is designed as a working environment for threat intelligence analysis rather than a dashboard or feed reader. Intelligence is ingested, processed, and structured locally, allowing analysts to move from raw reporting to actionable intelligence with minimal friction.
The platform emphasizes controlled processing and analyst-driven workflows. It operates independently of cloud infrastructure while still supporting optional enrichment and integration when required.
Core Capabilities
- Local Processing: Intelligence ingestion and storage handled entirely on-device
- Structured Summaries: Converts raw reports into concise intelligence
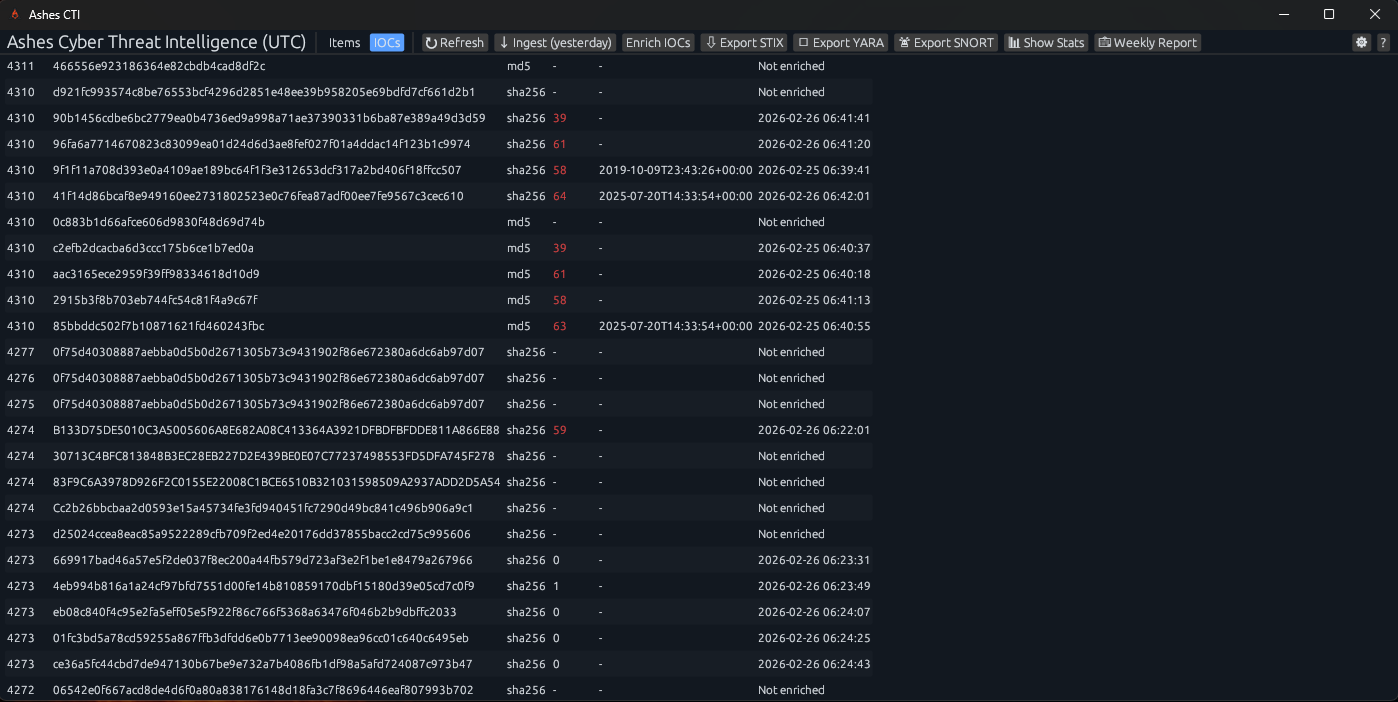
- IOC Extraction: Automatic identification of IPs, domains, hashes, and CVEs
- IOC Enrichment: Optional validation using VirusTotal and URLHaus
- MITRE ATT&CK Mapping: Technique mapping for operational context
- Export Support: STIX, TAXII, CSV, and JSON for integration
- Detection Rule Support: Extracts and manages YARA and SNORT rules from intelligence for direct use in detection workflows
In addition to intelligence consumption, the platform supports detection engineering workflows by enabling direct extraction and reuse of rules and indicators. This reduces the gap between threat intelligence and practical detection, allowing analysts to move from insight to implementation within the same environment.
Why Organizations Use It
Many threat intelligence platforms rely on cloud-based processing and continuous connectivity. In restricted or regulated environments, this introduces operational limitations.
Ashes CTI keeps processing local and focuses on producing validated, high-confidence intelligence before it is forwarded to downstream systems such as SIEM or EDR platforms. Structured processing, enrichment, and analyst-driven validation help reduce the volume of low-confidence or irrelevant data entering those systems.
What’s New in Version 1.3
- Dedicated IOCs view with enrichment details
- High-impact IOC highlighting
- Clickable indicators with VirusTotal integration
- Search and filtering across items and IOCs
- SNORT rule extraction support
- 6 UI themes and customization options
- Adjustable table views
- Built-in update checker
Where It Fits Best
- Government and defense environments
- Healthcare and regulated industries
- Enterprise SOC teams
- Air-gapped or restricted networks
- Analyst-driven security operations
Summary
Ashes CTI provides a structured and practical approach to threat intelligence through local processing, actionable outputs, and flexible integration. It complements existing security tools while remaining fully functional as a standalone system.